
- ITIL Basics
- ITIL - Home
- ITIL - Overview
- ITIL - Terminologies
- ITIL - Service Basics
- ITIL - Service Lifecycle
- Service Strategy
- ITIL - Service Strategy Overview
- ITIL - Service Strategy Roles
- ITIL - Strategy Generation
- ITIL - Service Portfolio Management
- Business Relationship Management
- ITIL - Demand Management
- ITIL - Financial Management
- Service Design
- ITIL - Service Design Overview
- ITIL - Service Catalogue Management
- ITIL - Service Level Management
- ITIL - Capacity Management
- ITIL - Availability Management
- ITIL - Service Continuity Management
- Information Security Management
- ITIL - Supplier Management
- Service Transition
- ITIL - Service Transition Overview
- ITIL - Project Management
- ITIL - Change Management
- Service Assets and Configuration Management
- Release and Deployment Management
- ITIL - Service and Validation Testing
- Service Operation
- ITIL - Service Operation Overview
- ITIL - Event Management
- ITIL - Incident and Request
- ITIL - Problem Management
- ITIL - Access Management
- Continual Service Improvement
- CSI Overview
- Service Reporting
- ITIL Useful Resources
- ITIL - Quick Guide
- ITIL - Useful Resources
- ITIL - Discussion
ITIL - Access Management
Overview
Access Management deals with granting access to authorized access while preventing access to non-authorized users.
Access Manager is the process owner of this process.
Key Points
Access Management is also known as ‘rights management’ or ‘identity management’.
Access Management process is executed by technical and application management functions.
Access Management can be initiated by Service Request through Service Desk
Value to Business
Access Management adds value to business in following ways −
Employees have right level of access to execute their jobs effectively
The ability to audit use of services and to trace the abuse of services.
Controlled access to services ensures that organization is able to maintain more effectively the confidentiality of its information.
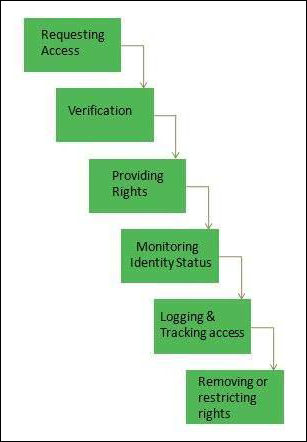
Access Management Process
Activates involved in Access Management are self-explanatory as shown in the following diagram −
To Continue Learning Please Login